Virtualization, Cloud, Infrastructure and all that stuff in-between
My ramblings on the stuff that holds it all together
Cannot logon to vCAC portal and you get Internal error when logging on as the root tenant
If you came to London VMUG last week and were one of the people who attended my vCAC real world session, you’ll have seen the demo gods not shining kindly on me as I couldn’t logon to my vCAC demo environment.
This was particularly annoying as I was testing it not 15mins before my session started and it was working 100%
With some quick on-stage debugging I found that I was unable to logon as any of the tenants on my vCAC deployment so was unable to show my cool demo 😦
After some further digging I found that I could logon to the root org https://vcacserver.net/shell-ui-app/ using the administrator@vsphere.local account but nothing else and I couldn’t logon to any of my tenant organisations despite the credentials being 100% correct.
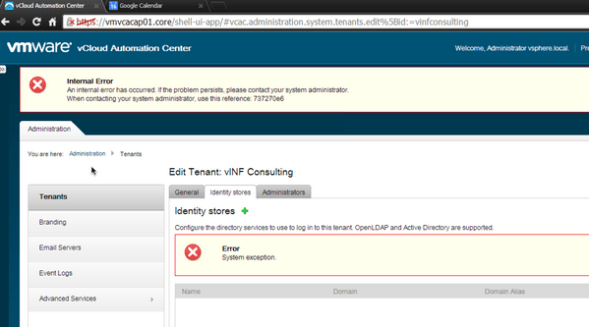
When logged onto the root org as administrator I could see the following error… which translates as “not good, your tenant has disapeared and I have an internal problem”
After some digging this seems this is a sort of time-bomb bug that has only been recently discovered, it occours after 90 days and will stop tenants being able to login using LDAP credentials.
When attempting to log into a tenant, a blank page is displayed with a Submit button in the upper left corner.
You receive a System Exception error when accessing the tenant identity store configuration page and the identity store configuration may have disappeared.
You cannot log in to a tenant using an LDAP account.
You are unable to add a new identity store configuration to the affected tenant.
The tenant identity store disappears from the SSO Administrator login.
This KB article details the issue and a temporary workaround
I assume a fix will follow in due-course.
In my case I worked out that it was exactly 90 days until about 15mins before my vCAC session started last Thursday – which is bad-timing taken to the extreme.
Once I have verified this fix in my environment and resumed access I will post a video of my intended real-world demo, where I’m using vCAC to deploy a VM and talk to a massive “enterprise system” via a REST API (e.g Twitter :)) – whilst an odd use-case this is an easy way of demonstrating the extensibility of vCAC (well, when it works anyway)
So, in summary if you have a vCAC implementation that you deployed since 6.0.1 came out you’re going to run into this install date +90 days.

As a follow-up, I can confirm that I appled this fix in my demo environment and it resolved the issue and I can access again 🙂
my setup
Identity appliance
Active Directory ised for tenant authentication
I followed the steps in the KB article for my scenario “Using SSO in the vCAC identity server”
if you used Kenny Colemans or Jad’s guide to setting up your POC this is the scenario you will have – the vCAC ID appliance uses it’s SSO to talk to vCenter and this is the internal password that will expire when you hit 90 days.
Even though my tenants are logging on using an external, unrelated Active Directory domain via LDAP this bug will still hit you.
I also noticed that I had some errors calling out to my workflows that used vCO, Again – Kenny the superstar to the rescue http://kendrickcoleman.com/index.php/Tech-Blog/vcac-error-connecting-to-vco-api-fixed.html
Pingback: Newsletter: May 25, 2014 | Notes from MWhite